Table of Contents
1. Introduction
Authentication service-accounts is one of three token based auth services. Currently there are three service accounts that can be authenticated with tokens:
- fleet-server
- kibana
- enterprise-search-server
Unfortunately you cannot create your own service account. For example for Logstash connection. Instead all these 3 are hardcoded with permission set using role_descriptor. Due to that limitation I will focus here on existing service accounts and specifically on kibana. I will show you how to start Elasticsearch, generate token and use that token for Kibana to connect with Elasticsearch. This does not require licensed version of ELK.
2. Start Elasticsearch
Important point here – please create volume and let it be populated with config catalog from Elasticsearch container so certificates created here will be available later on for Kibana.
docker run --rm \
--name elk \
--net kibana \
-d \
-p 9200:9200 \
-v elkconfig:/usr/share/elasticsearch/config/ \
docker.elastic.co/elasticsearch/elasticsearch:8.11.0
Once Elasticsearch is started please set password for elastic user.
docker exec -it elk bash -c "(mkfifo pipe1); ( (elasticsearch-reset-password -u elastic -i < pipe1) & ( echo $'y\n123456\n123456' > pipe1) );sleep 5;rm pipe1"
3. Create Service Account Token
Now you can create service account token for Kibana service account
curl -k -XPOST -u elastic:123456 "https://localhost:9200/_security/service/elastic/kibana/credential/token/forkibana?pretty"
example response below:
{
"created" : true,
"token" : {
"name" : "forkibana",
"value" : "AAEAAWVsYXN0aWMva2liYW5hL2ZvcmtpYmFuYTI6Yzd4Qm51RjJTeENCeG15bFZvUzVEdw"
}
}
If you do not specify name like ‘forkibana’ then you will get random name as a response.
4. Start Kibana
Normally you can start Kibana without any service account token and then once started use enrollment token generated during Elasticsearch startup. Instead you will run command with environment variable ELASTICSEARCH_SERVICEACCOUNTTOKEN that is taken by Kibana to set setting elasticsearch.serviceAccountToken.
This will let you run Kibana without manual actions.
docker run --rm \
--name kibana \
--net kibana \
-v elkconfig:/elkconfig \
-p 5601:5601 \
-e ELASTICSEARCH_SSL_VERIFICATIONMODE=certificate \
-e ELASTICSEARCH_HOSTS=https://elk:9200 \
-e ELASTICSEARCH_SERVICEACCOUNTTOKEN=AAEAAWVsYXN0aWMva2liYW5hL2ZvcmtpYmFuYTI6Yzd4Qm51RjJTeENCeG15bFZvUzVEdw \
-e ELASTICSEARCH_SSL_CERTIFICATEAUTHORITIES=/elkconfig/certs/http_ca.crt \
docker.elastic.co/kibana/kibana:8.11.0
Note that using “certificate” skips hostname verification.
Also http_ca.crt is used here to verify certs like truststore, this file was generated during Elasticearch container bootstrap and is accessible because of created volume elkconfig
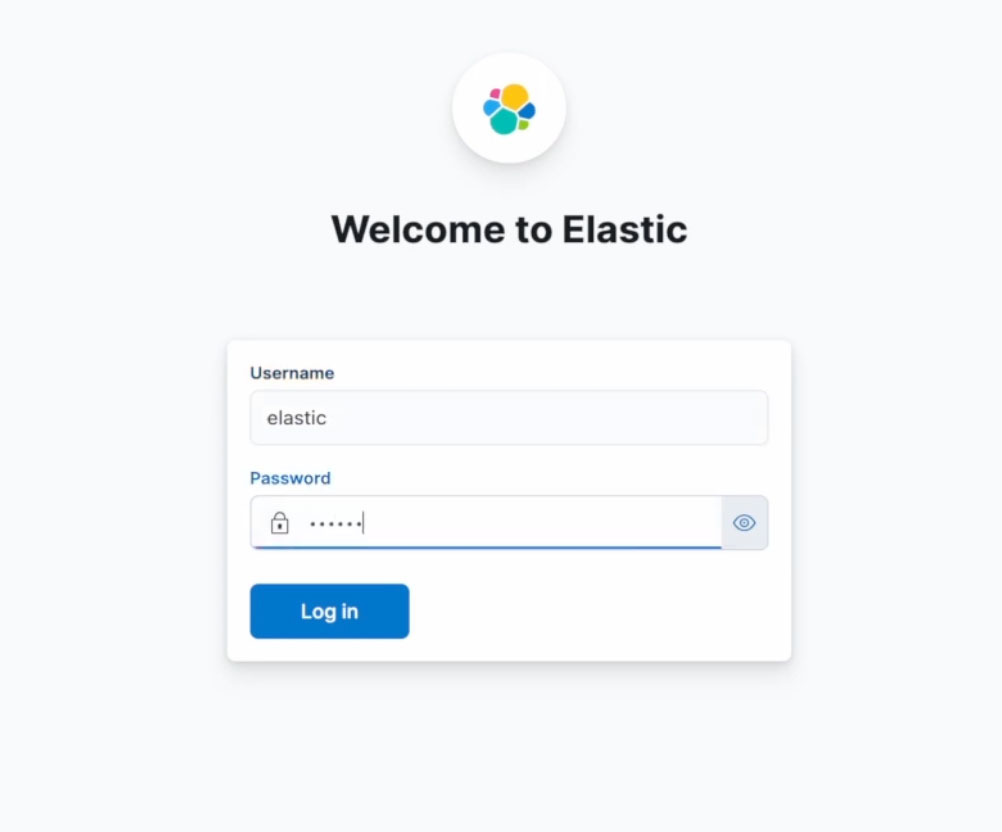
Goto http://localhost:5601/ address and now you can access your Kibana.
5. Can service account token create another token
This time only enterprise-search-server service account has enough privilege, cluster privilege ‘manage’ to be succinct. Others cannot create tokens. So if you create service account token for enterprise-search-server service account then it can create tokens independently.
#### Can token create another token
[manage_service_account,manage_security,all]
"elastic/enterprise-search-server": {
"role_descriptor": {
"cluster": [
"manage",
"manage_security"
],
{
"elastic/fleet-server": {
"role_descriptor": {
"cluster": [
"monitor",
"manage_own_api_key",
"read_fleet_secrets"
],
"elastic/kibana": {
"role_descriptor": {
"cluster": [
"monitor",
"manage_index_templates",
"cluster:admin/xpack/monitoring/bulk",
"manage_saml",
"manage_token",
"manage_oidc",
"manage_pipeline",
"manage_ilm",
"manage_transform",
"cluster:admin/xpack/security/api_key/invalidate",
"grant_api_key",
"manage_own_api_key",
"cluster:admin/xpack/security/privilege/builtin/get",
"delegate_pki",
"cluster:admin/xpack/security/profile/get",
"cluster:admin/xpack/security/profile/activate",
"cluster:admin/xpack/security/profile/suggest",
"cluster:admin/xpack/security/profile/has_privileges",
"write_fleet_secrets",
"manage_ml",
"cluster:admin/analyze",
"monitor_text_structure",
"cancel_task"
],
6. Summary
In this knowledge article you have learned how to use tokens for service accounts. You started Elasticsearch and later on you started Kibana that used created token in order to authenticate with server. This gives an idea how to automate startup of both with docker compose. Next step can be to secure Kibana and force it to connect with TLS to the user.
Have a nice coding!
One Comment