Hack WiFi with Samsung S10e phone
Table of Contents 1. Introduction How would you feel if you lost everything? Just imagine one day you pick up
Table of Contents 1. Introduction How would you feel if you lost everything? Just imagine one day you pick up
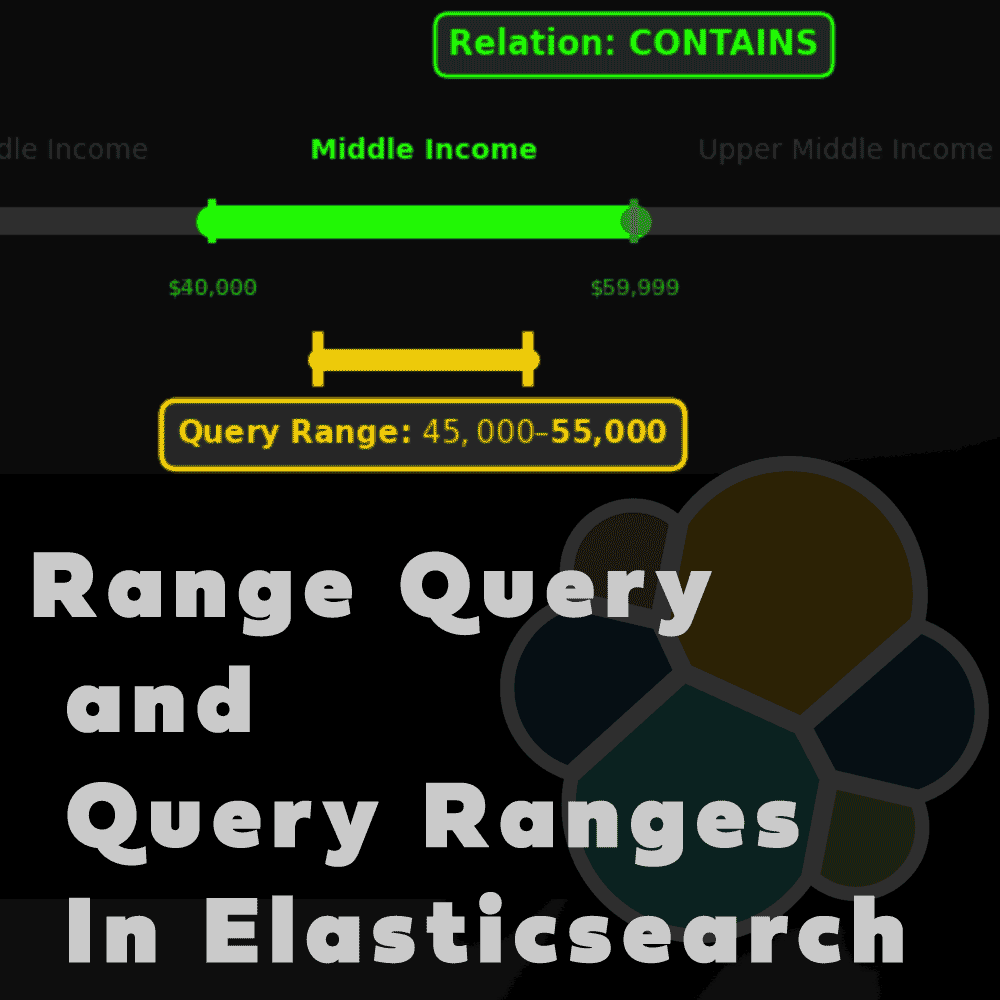
Table of Contents 1. Introduction You are running online shop with products and you have to allow users to filter

Table of Contents 1. Introduction I encounter many video hosting providers advertising so called basic DRM solution. Main purpose is

Table of Contents 1. Introduction Short background story. I was exploring website lookmovie2, page contain some movies that you can
Table of Contents 1. Introduction Have you ever wonder what happen when you update document in Elasticsearch? Here I am
Table of Contents 1. Introduction I came with idea of creating video course somewhere in 2022 and I started gathering

Table of Contents 1. Introduction I encounter many video hosting providers advertising so called basic DRM solution. Main purpose is
Table of Contents 1. Introduction Struggling with direct URL links to bunny.net videos? Cannot get back content you uploaded? This
https://youtu.be/lvfuk8e3h0Q Table of Contents 1. Introduction Authentication service-accounts is one of three token based auth services. Currently there are three
Table of Contents 1. Introduction Last time I was describing how to use service account kibana to access Elasticsearch with
Table of Contents 1. Introduction Token will never expire on it’s own but you can delete it via API. I
Table of Contents 1. Introduction In previous article I described how to authenticate to Elasticsearch using tokens. You were able
https://youtu.be/eOVzjC2N9TE Table of Contents 1. Introduction Last time I explained you how to login to Elasticsearch using API Keys as
Table of Contents 1. Introduction Docker in swarm mode brings secrets that allow to store sensitive information like passwords. Elasticsearch
Interview with Hacker Hacker ‘Achilles’ can access data without hacking Table of Contents 1. Background story So many times I